Navigating SOC 2 Type II Compliance
The process involved a rigorous evaluation and subsequent enhancement of our systems and practices, ensuring they exceed the standards set forth by the SOC 2 Type II classification. In this post, we’ll share more about SOC2 security standards and what we learned throughout the process.
Introduction: The Real Journey of Compliance and Security
At DraftWise, our path to SOC 2 Type II compliance was more than just ticking boxes and meeting industry standards; it was a deep dive into the essence of what we stand for – trust, security, and core commitment to safeguarding our clients' data. Each step in the compliance process was taken with a keen awareness of the responsibility we hold in managing and protecting the sensitive information entrusted to us by our clients.
This commitment to excellence in data security is ingrained in our culture. Before DraftWise, many of our engineering and product team leaders managed and built big data cyber security at Palantir Technologies. At DraftWise, this culture resonates through every aspect of our operations, reinforcing the trust our clients place in us.
The process involved a rigorous evaluation and subsequent enhancement of our systems and practices, ensuring they exceed the standards set forth by the SOC 2 Type II classification.
In this post, we’ll share more about SOC2 security standards and what we learned throughout the process.
Understanding SOC 2 and Type I vs. Type II
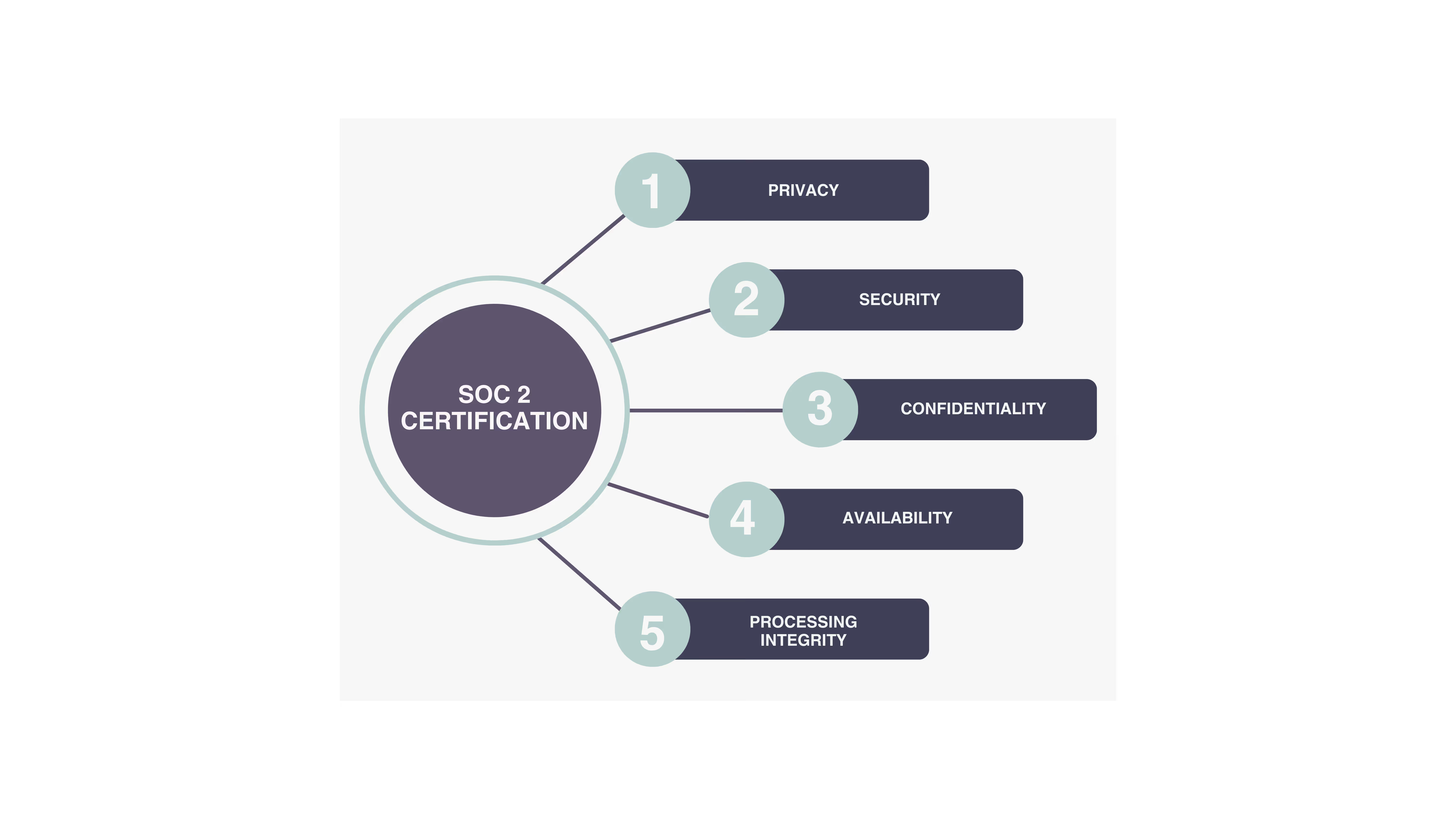
SOC 2, or System and Organization Controls 2, is a framework for managing and securing data that emphasizes customer privacy. Developed by the American Institute of Certified Public Accountants (AICPA), it's particularly relevant for technology and cloud-based organizations. This framework focuses on five principles: security, availability, processing integrity, confidentiality, and privacy.
There are two types of SOC 2 audits: Type I and Type II.
SOC 2 Type I: This type of report assesses an organization's systems and whether their design is suitable to meet relevant trust principles at a specific point in time. Essentially, it's a snapshot, evaluating if the company's systems are correctly set up to ensure security and privacy.
SOC 2 Type II: In contrast, a Type II report goes a step further. It examines the operational effectiveness of those systems over a period, typically ranging from six months to a year. This type of audit is more comprehensive, as it not only looks at the systems in place but also how effectively they function over time to protect and secure data.
In summary, while SOC 2 Type I is about the design of controls at a specific moment, Type II is about how those controls are operated over a longer period, ensuring ongoing compliance and security.
.avif)
Vanta and Advantage Partners
To meet the rigorous security standards of enterprise law firms, we first sought out a platform partner to help us establish our security and compliance foundation.
For us, Vanta provided an automated compliance platform that guided us through the labyrinth of SOC 2 preparation. Their tools and insights were pivotal in making sense of the complex web of compliance requirements. Their platform wasn't just about getting us through the audit; it offered continuous, live checks that kept us on track and compliant, not just for the audit but as an ongoing part of our operations. This real-time monitoring was crucial, ensuring that our practices didn't just meet the standards at a single point in time, but continuously to this day along with many other tools.
And then there was Advantage Partners, our third-party auditor, ensuring we were battle-ready and our defenses against data breaches were impenetrable. Their rigorous evaluations and feedback fortified our systems and practices, ensuring that we were not just compliant, but truly secure.
With the help and expertise of Vanta and Advantage Partners, what could have been a complex and overwhelming process was greatly simplified. Their guidance transformed our journey into one marked by confidence and assurance, replacing any anxiety and worry with a clear path forward. Their support was instrumental in not only achieving compliance but in doing so with a sense of preparedness and security.
Overcoming Obstacles in the SOC2 Process
Our journey wasn't without its dragons. From aligning our entire team with SOC 2 requirements to integrating Vanta's platform into our processes, each step required meticulous planning and execution. We learned quickly that communication and teamwork were crucial, much like in a well-oiled quest party. We juggled keeping up with our product development while embedding rigorous security practices into our daily operations.
Key Lessons and Challenges
The road to compliance was enlightening yet challenging. We learned the importance of:
- Building a Comprehensive Checklist: Identifying all requirements and preparing for them was essential. We focused on establishing robust privacy policies, setting up efficient processes for evidence gathering, and ensuring all teams were involved and aware of their roles in maintaining compliance.
- Choosing the Right Partner: Vanta's expertise in automating and simplifying the compliance process was invaluable. Their platform integrated seamlessly with our infrastructure, providing a clear overview of our compliance status and alerting us to potential issues.
- Automating Processes for Continuity: Maintaining SOC 2 Type II compliance is an ongoing effort. Utilizing Vanta's platform allowed us to monitor our compliance status continually and address issues proactively.
- Colleague Awareness and Training: We emphasized educating our employees on the importance of data security and responsible practices. This not only ensured compliance but also fostered a culture of security within the organization.
- Setting Realistic Milestones: Understanding that every organization's journey is unique, we set clear and achievable milestones, considering our specific needs and capabilities.
Benefits of SOC2 Compliance
Achieving SOC 2 Type II compliance has not only enhanced our security posture but also provided significant business benefits:
- Enhanced Trust with Clients: Our certification serves as a testament to our commitment to data security, building greater trust with our clients.
- Competitive Advantage: This compliance differentiates us in the market, especially when engaging with larger enterprises that value stringent data security measures.
- Improved Internal Processes: The journey helped us streamline our processes, ensuring a better understanding of roles and responsibilities related to data security within our team.
Beyond Compliance - What’s next for DraftWise
Our journey to SOC 2 Type II turned out to be a game-changer for us at DraftWise. By focusing so much on keeping data safe, we started seeing new ideas for our products and services that we hadn't thought of before. It's like this whole process of getting compliant opened our eyes to new ways to help our clients.
And the best part? Now, more companies want to work with us because they trust us more. This whole experience helped us grow and think about exciting new paths we can take in the future.
Our journey to SOC 2 Type II compliance was not just a compliance and security milestone; but it was a strategic investment in our future, reinforcing our reputation and setting a foundation for long-term trust and success.
.avif)